- ホーム
- > 洋書
- > ドイツ書
- > Mathematics, Sciences & Technology
- > Computer & Internet
- > internet, data communication, networks
Full Description
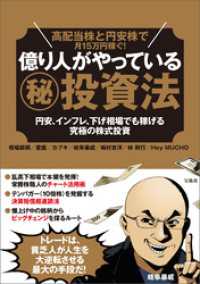
The 13th International Conference on Practice and Theory in Public Key Cryp- ' tography(PKC2010)washeldMay26-28,2010,attheEcoleNormaleSup' erieure (ENS) in Paris, France. PKC 2010 was sponsored by the International Associ- ' ation for Cryptologic Research (IACR), in cooperation with the Ecole Normale Sup' erieure (ENS) and the Institut National de Recherche en Informatique et en Automatique (INRIA). The General Chairs of the conference were Michel Abdalla and Pierre-Alain Fouque. The conference received a record number of 145 submissions and each s- missionwas assignedto at least 3 committee members. Submissions co-authored by members of the Program Committee were assigned to at least ?ve comm- tee members. Due to the large number of high-quality submissions, the review process was challenging and we are deeply grateful to the 34 committee m- bers and the 163 external reviewers for their outstanding work. After extensive discussions, the Program Committee selected 29 submissions for presentation during the conference and these are the articles that are included in this v- ume.
The best paper was awardedto Petros Mol and Scott Yilek for their paper "Chosen-Ciphertext Security from Slightly Lossy Trapdoor Functions. " The - view process was run using the iChair software, written by Thomas Baign' eres and Matthieu Finiasz from EPFL, LASEC, Switzerland, and we are indebted to them for letting us use their software. The program also included two invited talks: it was a great honor to have Daniele Micciancio and Jacques Stern as invited speakers.
Contents
Encryption I.- Simple and Efficient Public-Key Encryption from Computational Diffie-Hellman in the Standard Model.- Constant Size Ciphertexts in Threshold Attribute-Based Encryption.- Cryptanalysis.- Algebraic Cryptanalysis of the PKC'2009 Algebraic Surface Cryptosystem.- Maximizing Small Root Bounds by Linearization and Applications to Small Secret Exponent RSA.- Implicit Factoring with Shared Most Significant and Middle Bits.- Protocols I.- On the Feasibility of Consistent Computations.- Multi-query Computationally-Private Information Retrieval with Constant Communication Rate.- Further Observations on Optimistic Fair Exchange Protocols in the Multi-user Setting.- Network Coding.- Secure Network Coding over the Integers.- Preventing Pollution Attacks in Multi-source Network Coding.- Tools.- Groth-Sahai Proofs Revisited.- Constant-Round Concurrent Non-Malleable Statistically Binding Commitments and Decommitments.- Elliptic Curves.- Faster Squaring in the Cyclotomic Subgroup of Sixth Degree Extensions.- Faster Pairing Computations on Curves with High-Degree Twists.- Efficient Arithmetic on Hessian Curves.- Lossy Trapdoor Functions.- CCA Proxy Re-Encryption without Bilinear Maps in the Standard Model.- More Constructions of Lossy and Correlation-Secure Trapdoor Functions.- Chosen-Ciphertext Security from Slightly Lossy Trapdoor Functions.- Protocols II.- Efficient Set Operations in the Presence of Malicious Adversaries.- Text Search Protocols with Simulation Based Security.- Discrete Logarithm.- Solving a 676-Bit Discrete Logarithm Problem in GF(36n ).- Using Equivalence Classes to Accelerate Solving the Discrete Logarithm Problem in a Short Interval.- Encryption II.- Functional Encryption for Inner Product: Achieving Constant-Size Ciphertexts with Adaptive Securityor Support for Negation.- Security of Encryption Schemes in Weakened Random Oracle Models.- Fully Homomorphic Encryption with Relatively Small Key and Ciphertext Sizes.- Signatures.- Unlinkability of Sanitizable Signatures.- Confidential Signatures and Deterministic Signcryption.- Identity-Based Aggregate and Multi-Signature Schemes Based on RSA.- Lattice Mixing and Vanishing Trapdoors: A Framework for Fully Secure Short Signatures and More.