- ホーム
- > 洋書
- > 英文書
- > Computer / General
Full Description
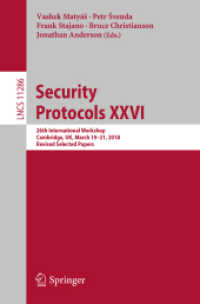
This book constitutes the thoroughly refereed post-workshop proceedings of the 21st International Workshop on Security Protocols, held in Cambridge, UK, in March 2013. The volume contains 14 revised papers with transcripts of the presentation and workshop discussion and an introduction, i.e.